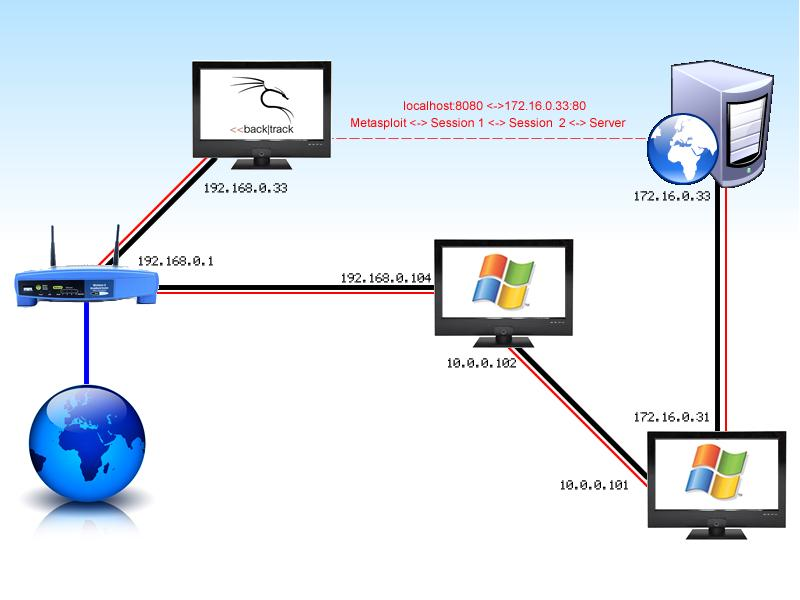
This screencast starts off by carrying out a "Man In The Middle" (MITM) attack, to inject traffic making the target vulnerable to "Cross Site Scripting" (XSS) which is linked to Metasploit's "Browser_AutoPWN" feature.
Upon being compromised, the attacker chooses to explore and exploit other devices which are attached to the internal network (Pivoting). To finalise, the attacker gains access to view the internal server via "Port Forwarding".
The attacker also installs backdoors into the network, allowing them to connect back at any stage.
Links
Watch video on-line:
Download video: http://download.g0tmi1k.com/videos_archive/Owning_Windows-XP_SP2_Vs._browser_autopwn.mp4
Download Script (iFrame_v2.zip): *Coming soon*
Scenario
This is the second video in a series of attacking Operating Systems and our target has now updated to Windows XP Service Pack 2, in the aid of seeking better security, after becoming compromised previously. ;)
Method
- Setup the attacker by starting network services, obtaining an IP address and starting PostgreSQL.
- Start metasploit and configure browser_autopwn to allow browser exploits.
- Setup Ettercap, prepare and compile filter.
- Once metasploit is ready, perform an ARP MITM attack.
- Wait for target to visit a web page.
- When a sessions has been establish, create a backdoor.
- Collect information on target.
- Start pivoting and scanning for other nodes.
- Perform a remote exploit.
- Create a backdoor, collect information, start pivoting and scanning... again.
- Once web server has been detected, port forward allowing for target to view content.
- Game Over.
Tools
- Ettercap – (Can be found on BackTrack 4-R2)
- iFrame.filter (Can either be downloaded from "links" at the top or manually created from the code below)
- Metasploit – (Can be found on BackTrack 4-R2)
- Internet Browser – (Firefox can be found on BackTrack 4-R2)
- Text Editor – (Kate can be found on BackTrack 4-R2)
iFrame.filter (v2)
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 30 31 32 33 34 35 36 37 38 39 40 41 42 43 44 | |
Commands
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 30 31 32 33 34 35 36 37 38 39 40 41 42 43 44 45 46 47 48 49 50 51 52 53 54 55 56 57 58 59 60 61 62 63 64 65 66 67 68 69 70 71 72 73 74 75 76 77 78 79 80 81 82 83 84 85 86 87 88 89 90 91 92 93 94 95 96 97 98 99 100 101 102 103 104 105 106 107 108 109 110 111 112 113 114 115 116 117 118 119 120 121 122 123 124 125 126 127 128 129 130 131 132 133 134 135 136 | |
Walkthough
The attacker approaches this attack differently by attacking the browser that is inbuilt to the operating system (OS) by using a collection of "browser exploits". They start up metasploit and configure it to create their evil page.
Once the evil web page has been set-up, it's a question of getting the target to visit this page. The attacker could try and "Socially Engineer" the target to view their web page (For example directly gets in contact either by placing a telephone call and saying the attacker is actually from technical support OR sends a spoofed email with their link disguised in the message). However, the attacker chooses to use XSS (Cross Site Scripting) to make the target visit the evil page when the target next views an infected page. The result being: the target visits the evil page without any knowledge of it happening.
The attacker could find what sites the target views (example in their lunch break/after their evening meal) and look for a weakness in those sites which would allow for XSS to be inserted. However, by doing this, it would be a "general/mass" attack which isn't ideal as the attacker specifically wants to attack just this target. Additionally, the attacker would also have to wait until the target visits that site (e.g. next lunch time).
To overcome this, the attacker decides to perform a Man In The Middle (MITM) attack, with the idea of speeding up the attack. As the attacker is on the same local area network (LAN) and subnet, the attacker has the option to perform "ARP poisoning" (Note: I plan to cover different methods of executing MITM attacks. Until then, see here).
This would allow the attacker to manipulate the target's traffic. In this instance, the attacker injects a hidden iFrame, with their XSS code that would link to the browser exploits.
The attacker is now ready and waits for the target to visit a vulnerable (1) web page so the target establishes a request to the evil page which responds with a collection of exploits.
Metasploit uses JavaScript to fingerprint (potentially detect the target's environment) for OS, Versions and installed software which use exploits that the target would be vulnerable too, as there is not much point responding with Firefox exploits if the user is using Internet Explorer!
Metasploit will automatically keep responding with remaining potential exploits until either a session is created or it hasn't got any more exploits left.
As it turns out, the target browser is vulnerable to "Internet explorer COM CreateObject Code Execution". We gained a session! As it turns out, 6 sessions were spawned, as all three injections methods work and the target refreshed the page... ;)
The first thing the attacker commands is to create a backdoor, which allows for access afterwards without the need of exploiting the target again as it might not happen next time because the target might upgrade / patch the vulnerability.
Metasploit has two methods to create a backdoor, one of which is to add a VBS (Visual Basic Script) file to start up (via registry) which will be triggered when either; the user logs in, the system starts up or the boot process initiates. In this instance, the attacker initializes the script to run when the user logs onto the computer, afterwards try to connect every 5 seconds back to the attacker.
In the video I restarted the target's computer to test the backdoor.
The attacker then starts to gather information on the target and when the attacker discovers that the target has another interface, chooses to explorer this (How deep does the rabbit hole go?)
As the attacker has got their foot in the door, they proceed to add the new subnet (10.0.0.0/8) of the new interface into metasploit, allowing the attacker to pivot from that computer. This allows the attacker to launch attacks from the compromised target.
This is useful for the attacker as they can launch attacks from inside the network instead of doing them remotely, which is beneficial as there is a chance that not all internal computers have their own firewall. This is something the attacker wouldn't be able to benefit from if they were doing a remote attack as they would have to worry about the WAN firewall.
The attacker then starts an ARP scan to see who else is connected. This reveals that another node is connected (10.0.0.101). The attacker would like to know what services the target has running and does a port scan. This shows that the target has port 139 open. As this port is commonly used for NetBIOS and the attacker is aware of an exploit (ms08_067_netapi) that the target might be vulnerable to, they give it a try...
The attacker is in! Just like before, the first thing the attacker proceeds to do is to create a backdoor, however this time chooses another method, which is to convert meterpreter to a service and to test it by connecting to it.
Again just like before, the attacker starts to collect information on the target and also notices that it has another interface. Like last time, the attacker adds the new subnet (172.16.0.0/12), starts pivoting from it to detect what else is out there. The result being that there is yet another node attached and a port scan shows that it could be running a web server. The attacker wants to see for themselves, that they want to view the content of this internal server.
The attacker set ups port forwarding which allows them to view the remote content locally.
GAME OVER
(1): The iFrame can be injected differently into each page as it depends on how the page is coded.
When I was developing the filter, the one used in this method had the highest injection success rate with the lowest count of broken pages.
The filter looks for "</title>" and "body>" tags (which covers "<body>" and "</body>"). Therefore, there are 3 possible places to inject into.
It may not work on EVERY page for a few reasons, much as:
- As the user may be using cache local version.
- The page doesn't have a title. E.g. doesn’t use "
<title></title>". - The page has extra content in the body tags. E.g. "
<body id=”something”>" - Uses spaces to break up tags. e.g. “
< / body >"
The top half of the script makes sure the web page is sent in plain text – and not compressed, which increases the chances of injection for the attacker.
Notes
- The video recording software glitched making the mouse icon appear stuck in a fix position, as a result I hid the cursor. (First time recording it, virtual box crashed near the end, I didn't realised the mouse issue until I started editing it and I didn't really want to record it for a third time!)
- All targets were using Windows XP Pro. Other than having their service packs installed, no other updates have been applied and everything is set at their default values.
- Browser_autopwn may not work on your chosen target's web browser - Target in the video is running Windows XP SP2
- Windows XP SP2 (First target) has a firewall and it's enabled, however, as the attack is reversed and the target connects back to the attacker which allows the connection happen.
- Windows XP SP1 (Second target) has a firewall but its disabled by default (fail!). Therefore it doesn't matter too much about doing a bind connection, where the target is the server, allowing the attacker to connect.
- The Windows XP SP1 (Second target) was only placed to show you can keep on pivoting once you have gained internal access. This is the reason why I didn't want to spend much time on this section, therefore tests had been done prior to the video hence it was already known that the exploit would work.
- As the target is making a connection out to the evil page (without the target knowing it!) it bypasses window's in-built firewall making it not a issue. However some 3rd party firewalls and or a Intrusion Detection System (IDS) may detect it.
- This is a poor network layout, however the MITM could be done remotely (not by doing ARP poisoning) as well as the browser exploits could be hosted somewhere other than on the attackers computer.
Song: Edvard Grieg - In the Hall of the Mountain King & Richard Wagner - Ride Of The Valkyries & Rossini - William Tell Overture (Finale) & Tchaikovsky - '1812' Overture
Video length: 12:04
Capture length: 35:11
Blog Post: https://blog.g0tmi1k.com/2011/01/owning-windows-xp-sp2-vs/
Method
- Setup the attacker by starting network services, obtaining an IP address and starting PostgreSQL
- Start metasploit and configure browser_autopwn to allow browser exploits
- Setup Ettercap, prepare and compile filter,
- Once metasploit is ready, perform an ARP MITM attack
- Wait for target to visit a web page
- When a sessions has been establish, create a backdoor
- Collect information on target
- Start pivoting and scanning for other nodes
- Perform a remote exploit
- Create a backdoor, collect information, start pivoting and scanning... again
- Once web server has been detected, port forward allowing for target to view content
- Game Over